Несколько десятилетий назад использование первой программы в прикладных целях дало начало процессу цифровизации. Цифровизацией будем называть всё, связанное с использованием программных средств, двоичного кода, информационных технологий. Сначала с помощью программ совершались вычисления, затем программирование распространилось на технологические процессы. Информационные технологии проникли почти во все аспекты бизнеса, и этот процесс будет продолжаться. Уже сейчас электронная торговля составляет самую большую долю экономики. Цифровизация менеджмента позволяет гибко управлять предприятием, передавая часть функций программам. Цифровая телемедицина ставит диагнозы с помощью самообучающихся нейросетей. Цифровая видеостудия снимает сериалы на основе анализа предпочтений зрителей. Цифровое такси… ну, вы знаете. Евангелисты предрекают, что дни бизнесов, которые не пожелают оцифровываться, сочтены.
У информационной безопасности, казалось бы, нет своего содержания, она обеспечивает нормальное функционирование основного бизнес-процесса. Но, с другой стороны, его защита - это настолько важный вопрос, что служба безопасности из вспомогательного подразделения становится чуть ли не основным. И хотя киберугрозы не несут прямого вреда здоровью, всё же безопасность транзакций, защита от хищения, сохранность дорогостоящего оборудования - вопрос жизни и смерти предприятия. В случае взлома медицинских информационных систем существует вероятность нанесения вреда здоровью и жизни людей. А если мы в ближайшем будущем, как нам обещают футурологи, перейдем на вживляемые чипы, по опасность станет вполне осязаемой. В связи с этим именно соображения информационной безопасности могут поставить светлое цифровое будущее под вопрос.
Цифровая трансформация - это не просто передача компьютеру каких-то функций. Также далека от цифровизации и лоскутная автоматизация, когда для каждой части подбирается отдельное решение, и эти решения плохо между собой дружат. О цифровой трансформации можно говорить только в том случае, если мы получаем новое качество управления, аналитики, прогнозирования. Есть компании, которые сделали цифровизацию основой своей идеологии, это привело к переосмыслению рынка, новому отношению к клиентам, дало новые инструменты и подходы. Большинство же руководителей стремятся с помощью цифровых инструментов сделать более эффективным традиционный бизнес.
Берите столько, сколько сможете переварить
Есть несколько областей, где цифровые средства уже надежно обосновались и стали всем привычны: это бухгалтерия и финансы, управление технологическим процессом, некоторые охранные функции. Понемногу завоевывает позиции электронный маркетинг, особо продвинутые компании достигли высот по цифровому управлению продажами и отношениями с клиентами. Цифровизация информационной безопасности имеет фрагментарный характер. Собственно, сама тема информационной безопасности у нас еще довольно плохо приживается. Чаще всего дело ограничивается контролем интернет-трафика или доступа к внутренним электронным ресурсам. Тогда как именно внедрение системы информационной безопасности чаще всего позволяет говорить о цифровизации управления.
История проникновения компьютеров в нашу жизнь дала нам иллюзию всемогущества, тогда как чаще всего мы осваиваем только поверхностные возможности. Переведение процессов в электронный вид позволяет лучше понимать то, чем вы управляете. В цифровой среде каждое действие оставляет след, нужно только собрать эту информацию, проанализировать ее и сделать выводы. Современный этап развития технологий позволяет перейти к новому уровню использования цифровых средств, но для этого требуется некоторая перестройка мозгов.
С чего начать
Управление каждым бизнес-процессом или функцией по отдельности дает лоскутность восприятия, мы перестаем понимать, как части связаны между собой. Чаще всего они и не связаны, и приходится титаническими усилиями удерживать в голове различные параметры и притягивать их друг к другу. Первый шаг к тому, чтобы перевести управление на цифровые рельсы, - понять, что уже есть, какие программные средства используются, составляют ли они систему или живут каждый своей жизнью. На основе этого аудита можно делать выводы, какие есть пробелы и как их заполнять.
Второй шаг на пути цифровизации - приведение всей инфраструктуры к общим стандартам управления. На рынке мы видим два подхода к решению этой задачи. Первый - покупать максимально возможное число ПО у одного производителя (вы догадываетесь, какого). Но такой подход имеет свои очевидные минусы, главный из которых - монополизация рынка. Современный уровень развития технологий и общества позволяет требовать большего. Поэтому второй подход, который набирает всё большие обороты, - это программное обеспечение с открытым кодом - open source. Смысл его не только в доступности исходного кода для корректировки и доработки. Главный принцип - устанавливаются общие стандарты, протоколы взаимодействия, которые позволяют программному обеспечению быть совместимым, а его потребителям - строить свою собственную цифровую среду, дорабатывая ее под свои нужды. А если в опенсорсных продуктах делать упор на отечественные разработки, то есть надежда, что уменьшится влияние международного кибертерроризма на наши дела.
StaffCop как инструмент цифровизации
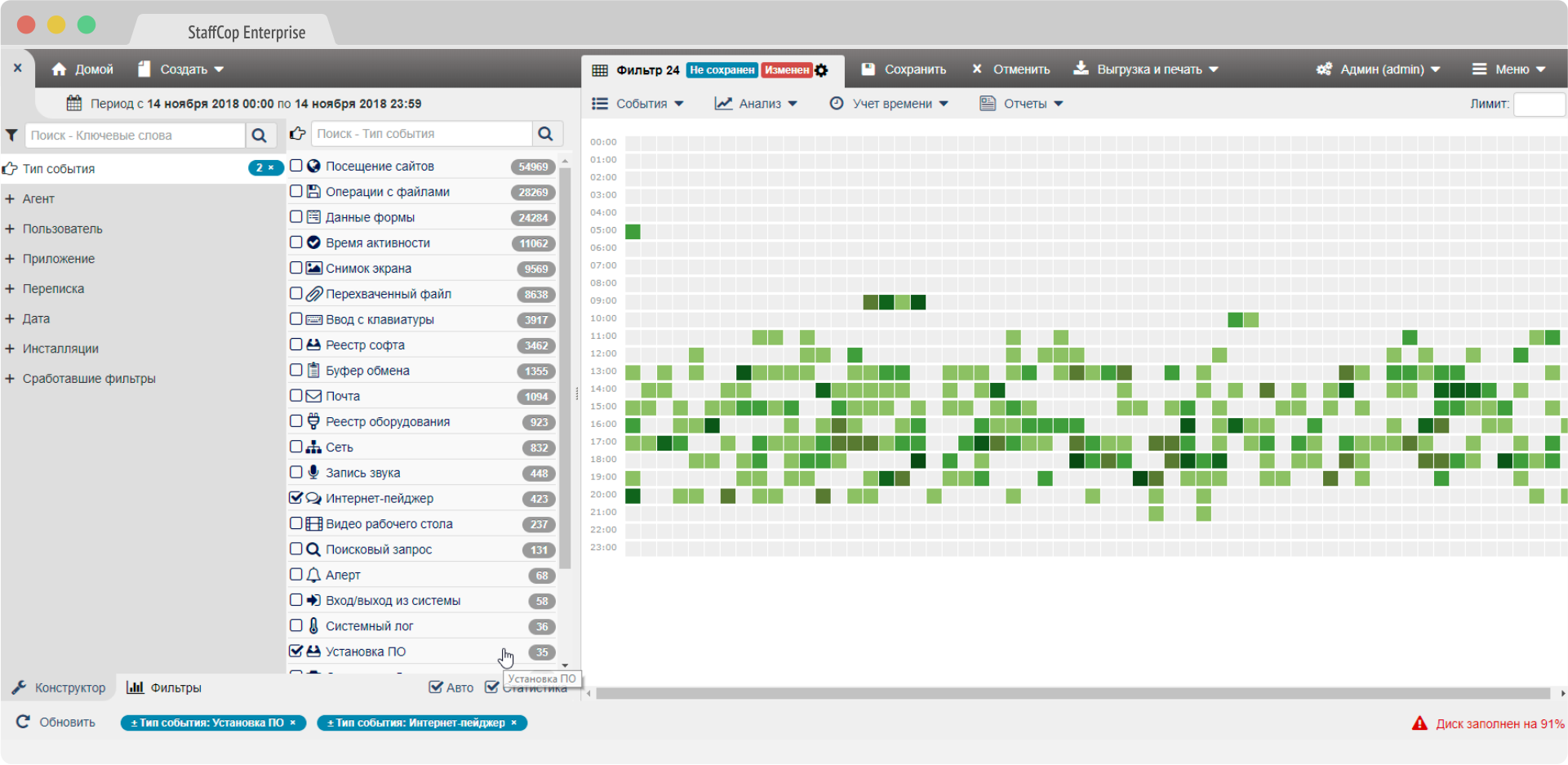
Использование open source имеет еще и тот плюс, что позволяет избежать лишних трат на продление лицензий, приобретение новых программных решений и пр. Вы единоразово приобретаете базовый продукт и пользуетесь им, так что цена владения перестает непредсказуемо расти. Именно поэтому компания StaffCop с самого начала основывала свои разработки на продуктах open source. Программа StaffCop Enterprise - это система мониторинга действий пользователей, которую можно использовать как одну из главных частей системы информационной безопасности. В ней реализован актуальный на сегодняшний день принцип защиты информации - беспериметровая архитектура ИБ. Это значит, что неважно, где находятся ваши сотрудники и соединены ли они с вами внутренней сетью. Если они имеют выход в интернет, StaffCop может работать.
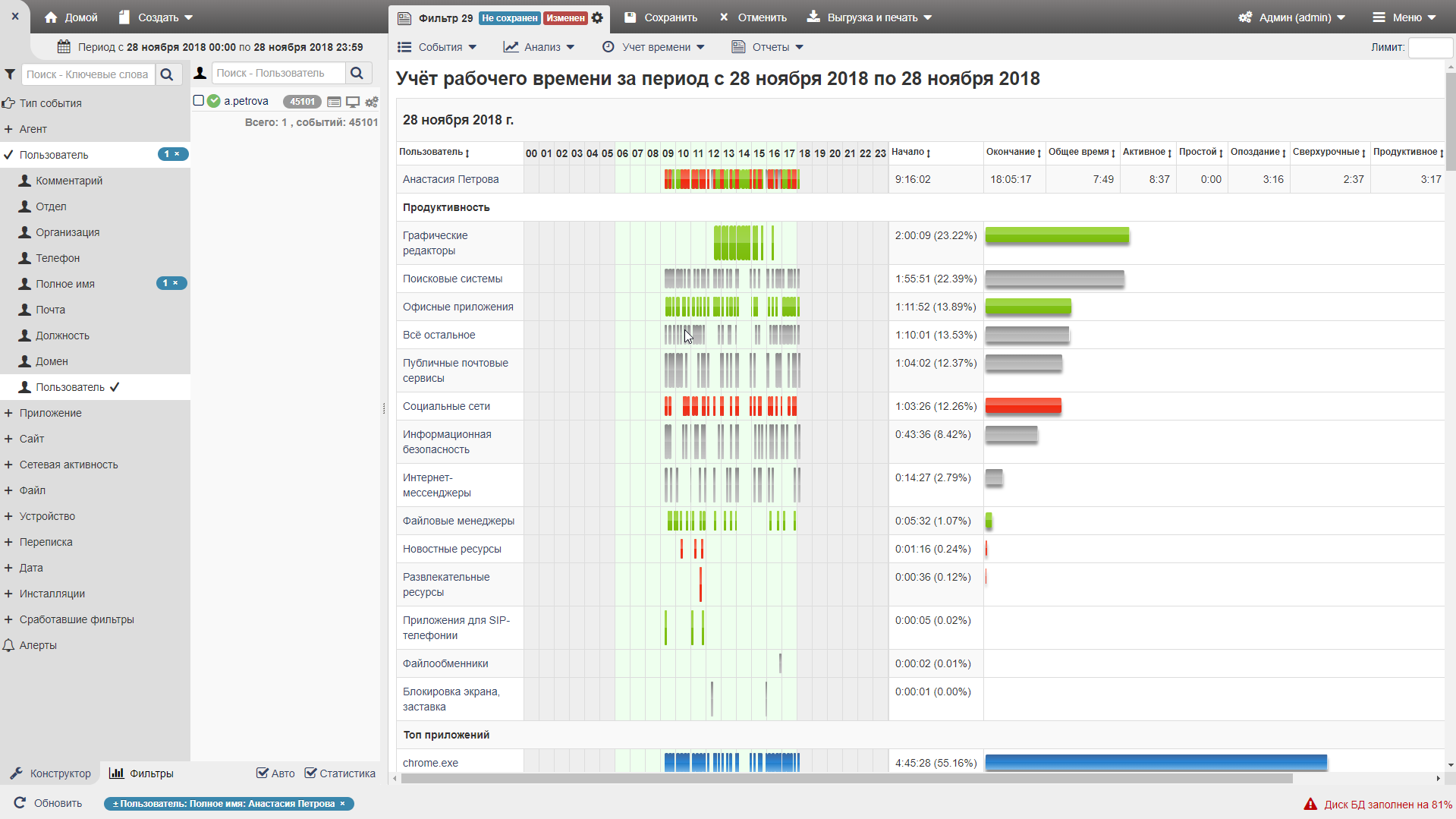 Программа собирает логи для расследования инцидентов информационной безопасности, систематизирует их с помощью продвинутых аналитических инструментов и имеет много других полезных функций. Она может отслеживать коммуникации и моральный климат в коллективе, на основании анализа поведенческих аномалий прогнозировать критические ситуации, защищать коммерческую тайну, администрировать удаленные рабочие места, и, следовательно, не только системно управлять информационной безопасностью, но и давать много ценной управленческой информации руководителям всех уровней.
Программа собирает логи для расследования инцидентов информационной безопасности, систематизирует их с помощью продвинутых аналитических инструментов и имеет много других полезных функций. Она может отслеживать коммуникации и моральный климат в коллективе, на основании анализа поведенческих аномалий прогнозировать критические ситуации, защищать коммерческую тайну, администрировать удаленные рабочие места, и, следовательно, не только системно управлять информационной безопасностью, но и давать много ценной управленческой информации руководителям всех уровней.
В сущности, это универсальный инструмент, который может быть основой цифровизации для нецифровых или частично оцифрованных бизнесов. Например, одна из дополнительных функций - аудит информационной инфраструктуры: можно получать перечень всего работающего оборудования и всех программ, установленных на нем. Это не только покажет вам картину цифровизации вашего предприятия, но и позволит зафиксировать, если сотрудник свинтил дорогую видеокарту и вместо нее поставил дешевую. Так же и с программным обеспечением. Система мониторит наличие и использование программного обеспечения. Она даст сигнал, если сотрудник будет закачивать вредоносную программу или майнить биткоины в рабочее время.
Кроме того, StaffCop отслеживает трудовую дисциплину и выполнение KPI: сколько писем и звонков сделал сотрудник за день, работает он в офисных программах или сидит в соцсетях. Кстати, работа в соцсетях для SMM-специалиста является основой обязанностью, и такие нюансы также можно настроить с помощью StaffCop. Для многих сотрудников факт отслеживания их занятости в течение дня становится стимулом повысить трудовую дисциплину.
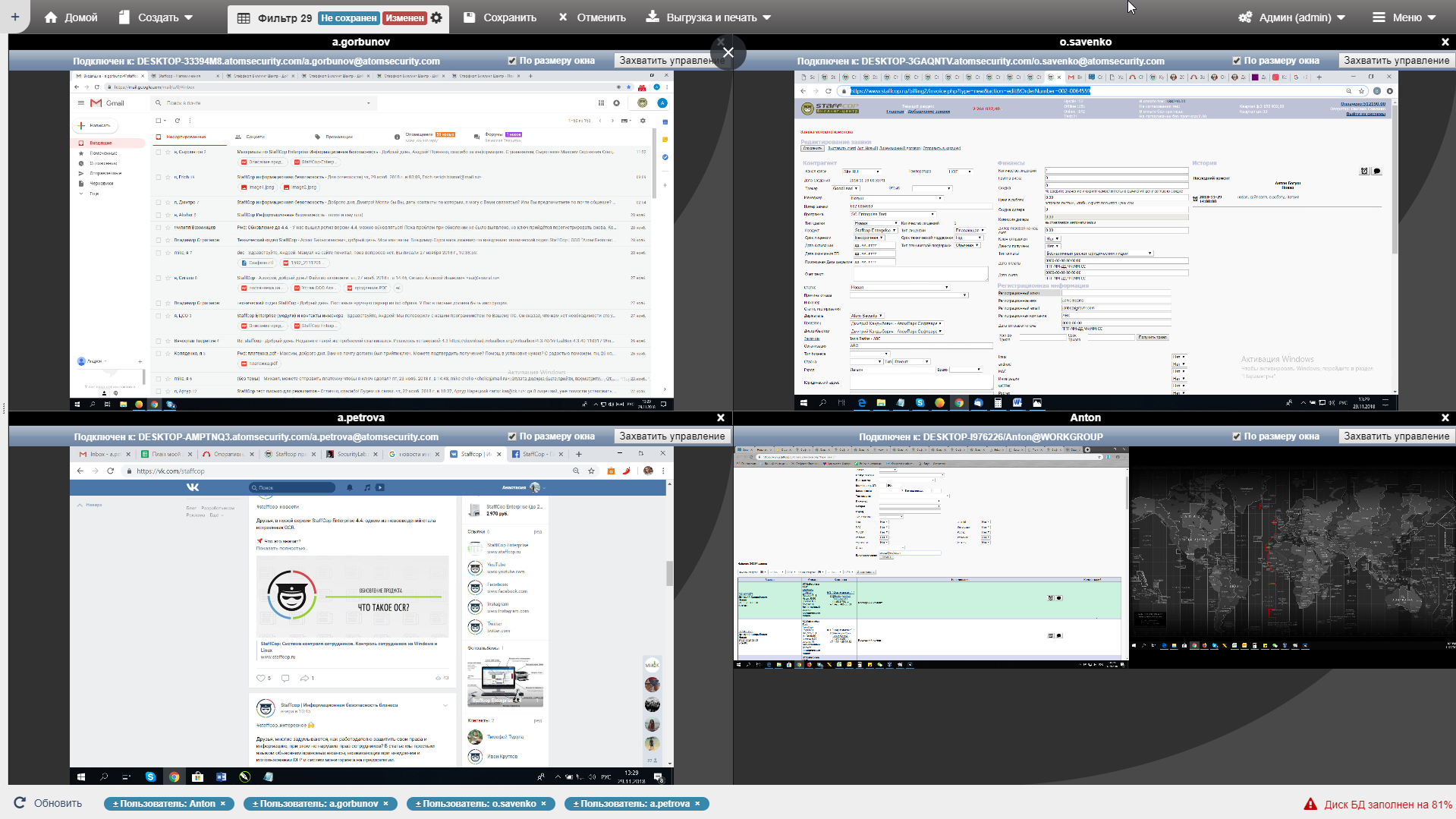 Системность заложена и в самой архитектуре StaffCop. Программа изначально настраивается на бесконфликтное взаимодействие с другими элементами информационной инфраструктуры, а если возникают неполадки с обновленными версиями сторонних программ, служба поддержки ликвидирует их в кратчайшие сроки. Кроме того, само решение StaffCop Enterprise включает в себя функции, решающие сопутствующие задачи. Например, вам не придется приобретать дополнительные программы, такие, как Teamviewer и прочие средства администрирования, прокси и другие.
Системность заложена и в самой архитектуре StaffCop. Программа изначально настраивается на бесконфликтное взаимодействие с другими элементами информационной инфраструктуры, а если возникают неполадки с обновленными версиями сторонних программ, служба поддержки ликвидирует их в кратчайшие сроки. Кроме того, само решение StaffCop Enterprise включает в себя функции, решающие сопутствующие задачи. Например, вам не придется приобретать дополнительные программы, такие, как Teamviewer и прочие средства администрирования, прокси и другие.
 Несмотря на то, что информационная безопасность не имеет своего содержания, она снижает издержки и повышает эффективность основного направления деятельности. Кроме того, никакая цифровизация не заработает без должного уровня информационной безопасности.
Несмотря на то, что информационная безопасность не имеет своего содержания, она снижает издержки и повышает эффективность основного направления деятельности. Кроме того, никакая цифровизация не заработает без должного уровня информационной безопасности.